Overview
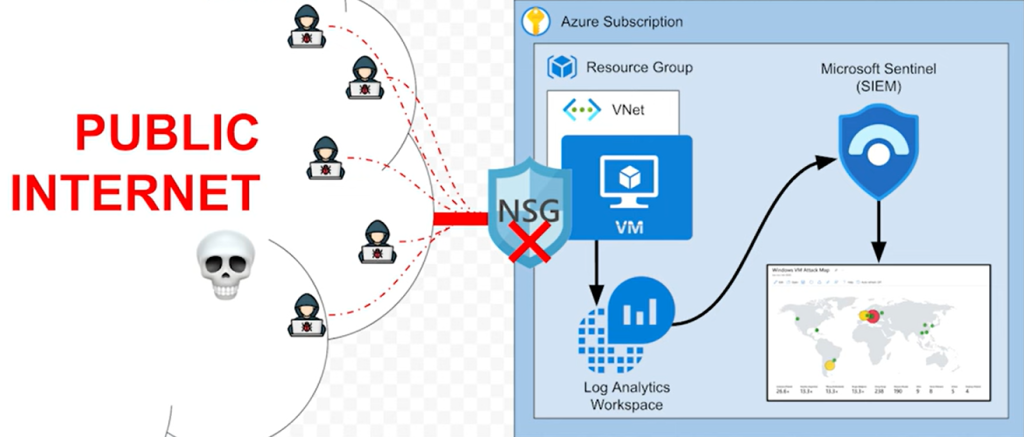
In this project, I set up a basic Security Operations Center (SOC) in Azure. The goal was to create a cloud-based environment capable of detecting real-world cyber threats. By configuring a virtual machine (VM) as a honeypot, forwarding logs to a centralized repository, and integrating Microsoft Sentinel, I could analyze live attack data and visualize potential security threats.
Visual of Project Setup
Project Steps
1. Setting Up the Azure Environment
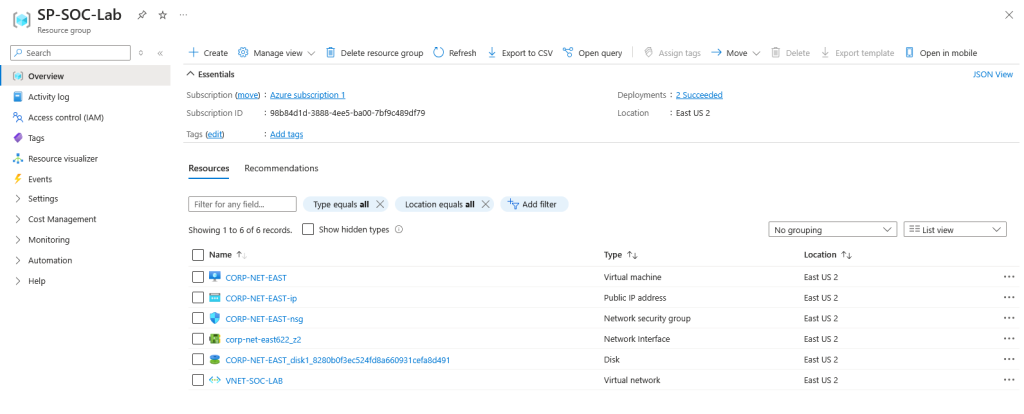
To begin, I created resource group and virtual network. The importance of selecting the correct resource group and region for your virtual network enhances organization and resource management within Azure. This helps in monitoring and controlling cloud resources effectively.
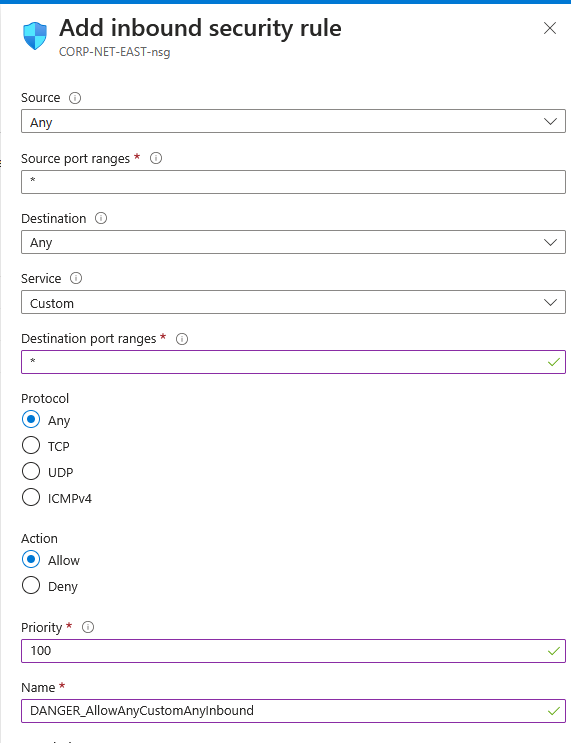
Following that I deployed a Virtual Machine (VM). I intentionally exposed it to the internet to attract malicious login attempts, simulating a real-world attack scenario. This is not recommended but to gather this data, I had to adjust security settings. To do this, I created an Inbound Security Rule for the VM in Azure which is crucial for allowing traffic. This process configures various parameters such as source, destination, and priority settings. I also disabled the Windows Defender firewall on the VM, which is dangerous but intentional for this purpose.
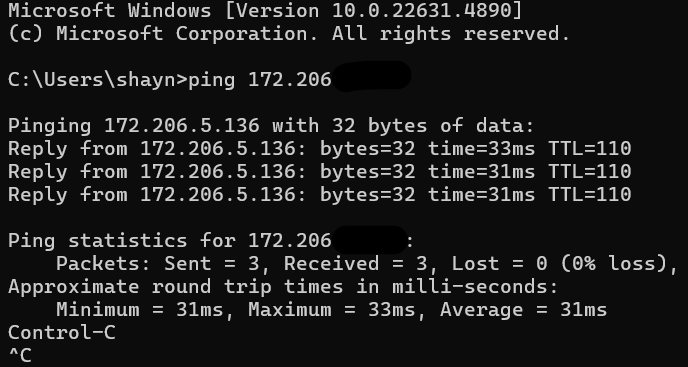
I verified connectivity by pinging the VM. This step ensures that the machine is reachable over the public internet, indicating potential vulnerability. After that, I went to Event Viewer to confirm my activity. Understanding the Event Viewer allows users to navigate through various logs related to security events on their Windows machine. It provides insights into both successful and failed login attempts. Event IDs play a significant role in identifying specific security events, such as ID 4625 which indicates a failed login attempt. Users can filter logs by these IDs to focus on relevant security incidents.
2. Configuring Log Analytics Workspace
To ensure proper monitoring, I set up a Log Analytics Workspace within Azure. This allowed me to collect system logs and security events from the honeypot VM for further analysis. Integrating with Azure and using Microsoft Sentinel enhances the ability to forward logs for deeper analysis. This setup enables users to monitor attempted breaches in real-time effectively.
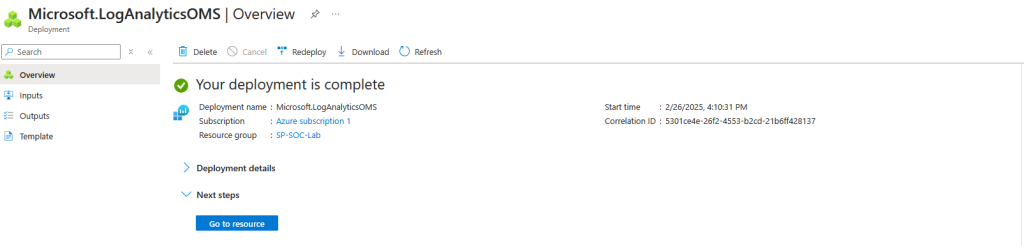
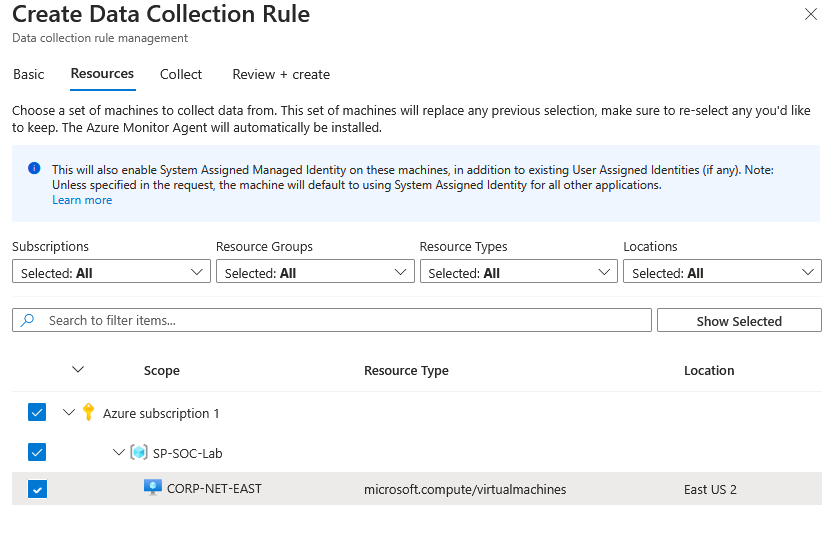
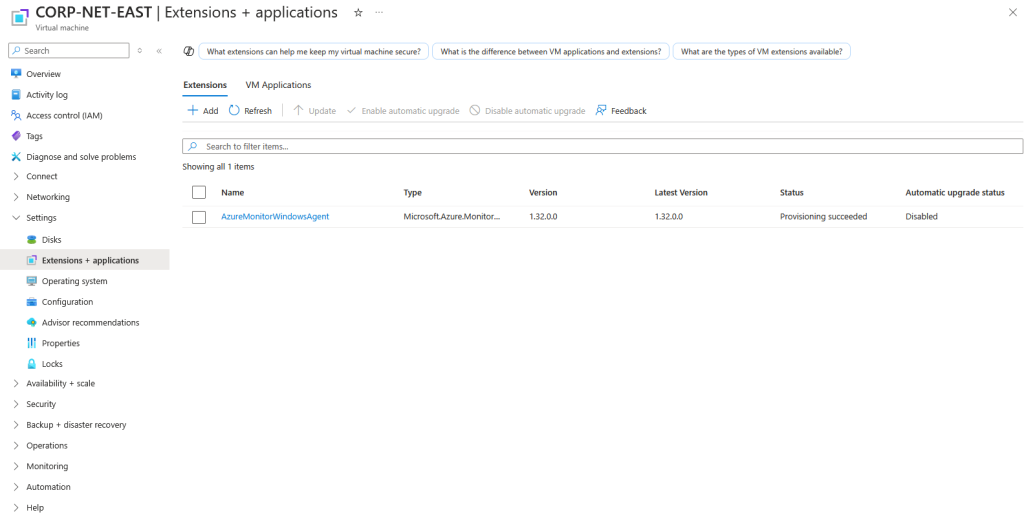
The installation and configuration of the Azure monitoring agent on a virtual machine is crucial for forwarding logs to a log analytics workspace. This process ensures that security events are properly monitored and recorded for analysis. For this to happen, a data collection rule is required to manage how logs are forwarded from the VM to Azure Log Analytics.
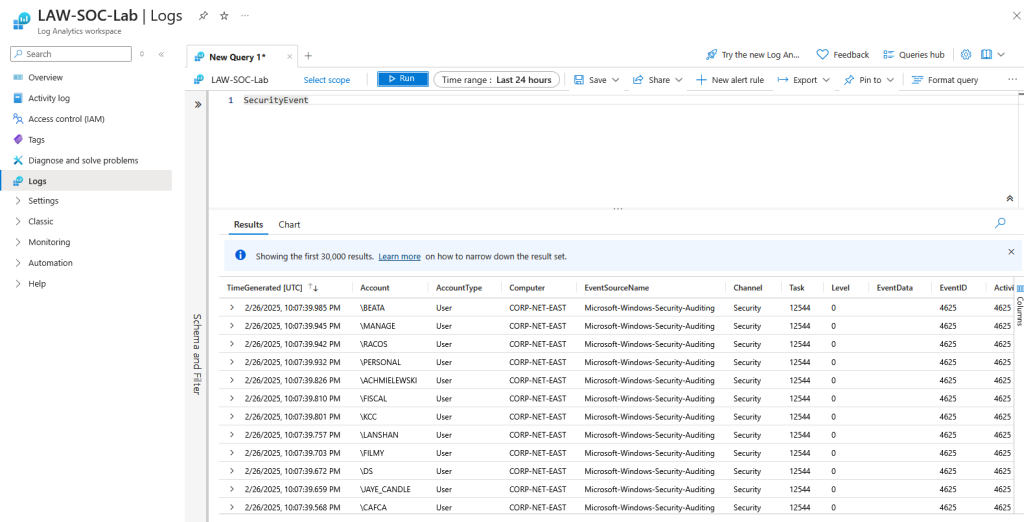
Once completed, we can see the data and explore using KQL (Kusto Query Language) which helps users filter and analyze the logs effectively, allowing for targeted investigation of security events. This capability enhances the overall monitoring process.
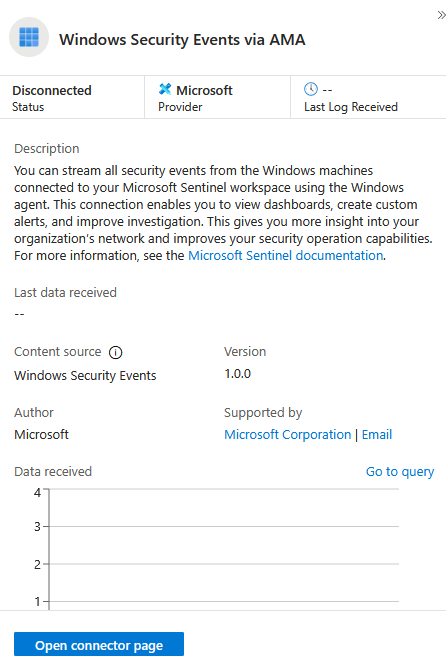
3. Forwarding Logs to Microsoft Sentinel
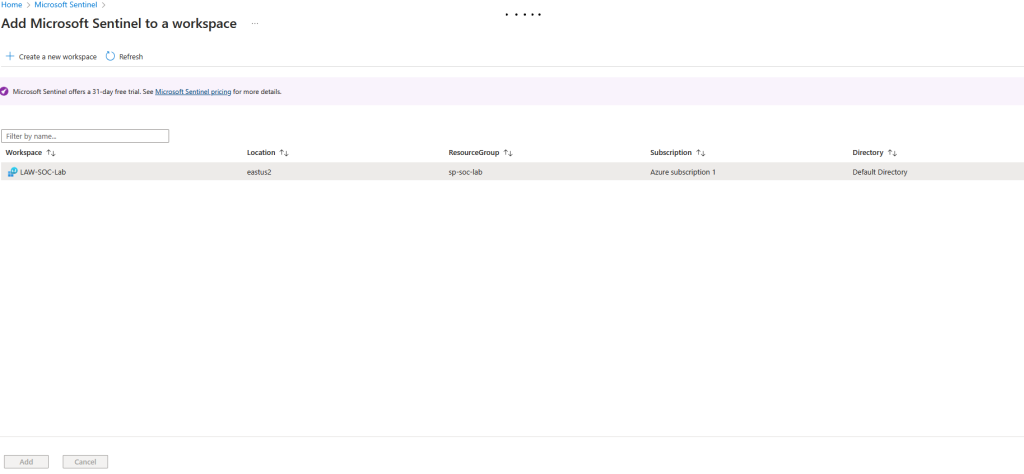
Next, I integrated Microsoft Sentinel, Azure’s cloud-native SIEM (Security Information and Event Management) solution. By forwarding logs from the VM to Sentinel, I could centralize security data and leverage its built-in detection capabilities.
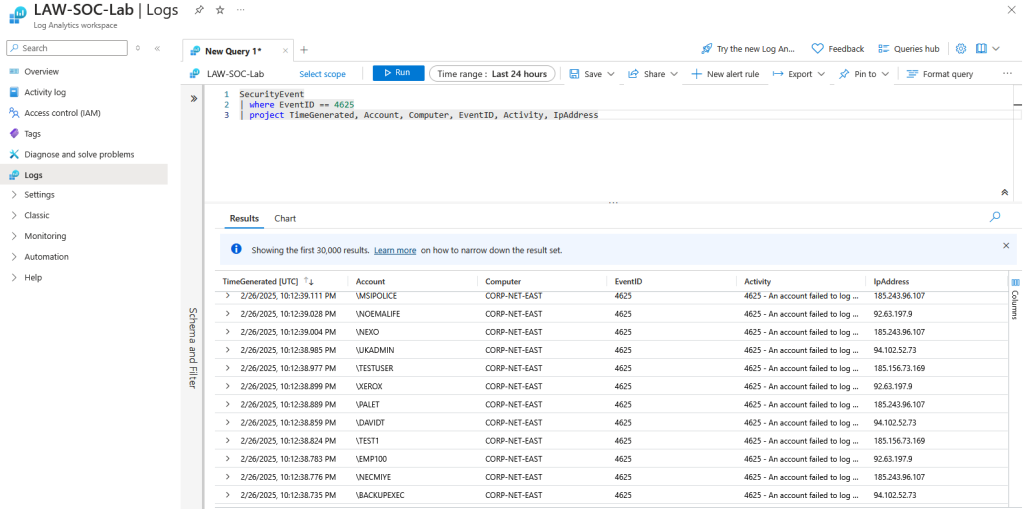
4. Querying Failed Login Attempts & Attack Sources
Using Kusto Query Language (KQL) within Sentinel, I analyzed failed login attempts, identifying patterns and potential attackers. By extracting source IPs and geolocation data, I gained insights into the origin of these attacks.
I can see the data and explore using KQL (Kusto Query Language) which helps users filter and analyze the logs effectively, allowing for targeted investigation of security events. This capability enhances the overall monitoring process. The significance of filtering log data is emphasized, allowing users to focus on relevant security events while ignoring unnecessary information. This process aids in identifying potential threats effectively.
The rapid accumulation of failed login events from a specific IP address highlights the need for prompt security measures. Understanding the origin of these attempts provides context for potential risks. The importance of geographic data in security analysis is discussed, as it enables the identification of attackers’ locations. This information can be leveraged to enhance security responses and countermeasures.
5. Building a Real-Time Attack Map
To visualize hacker activity, I created an attack map that displayed live intrusion attempts. This provided an interactive way to track where threats were coming from and demonstrated the importance of proactive threat monitoring.
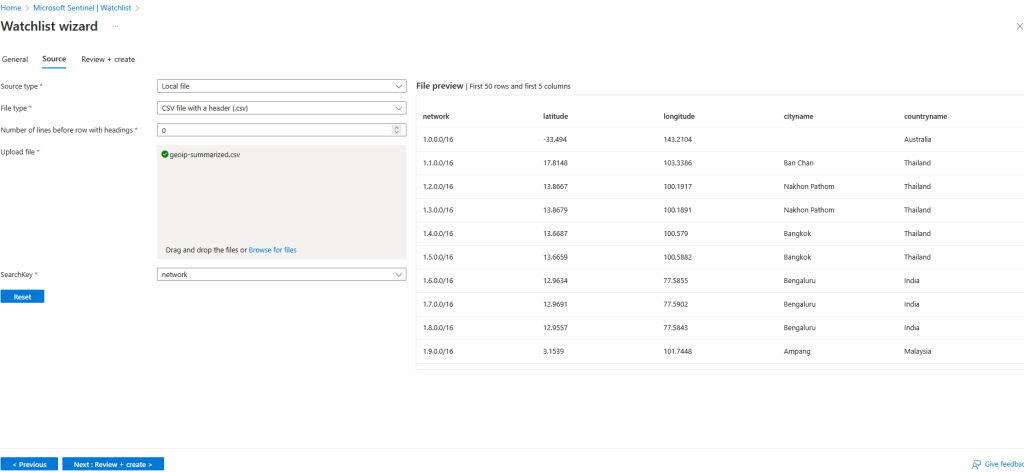
The first step to achieve this is to set up a watch list in Sentinel which is essential for monitoring network activity. In this scenario, I imported a spreadsheet containing geographical information such a location, longitude, latitude, etc. Once set up, I can query the watch list analyze login failures, and identify security threats.
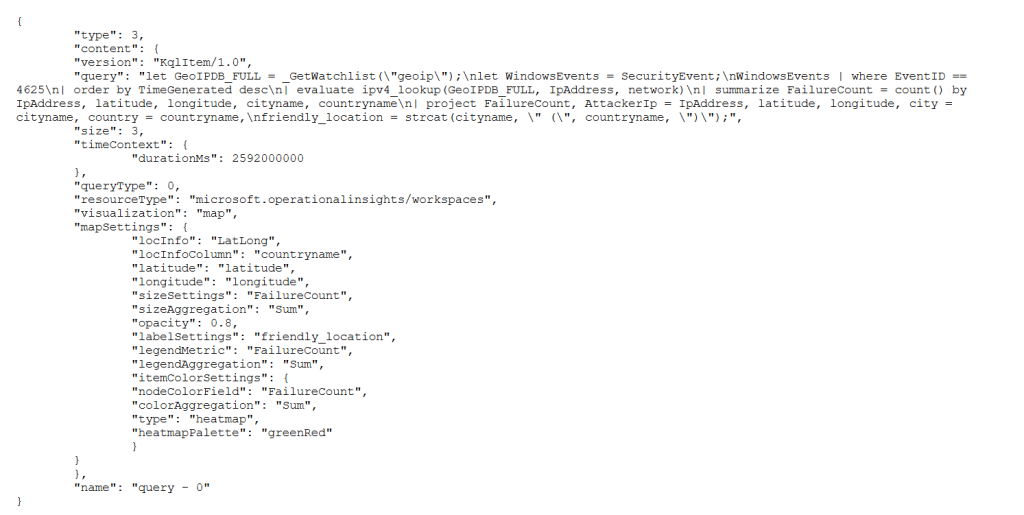
Once the watchlist was created, I moved to the final part creating an attack map by analyzing login failures from the virtual machine. Within Sentinel, I created a workbook and added a query element. From there, I pasted a JSON file to create the attack map, which can be seen below. Following that setup, I was able to observe the query and map settings to look at how I’d prefer it.
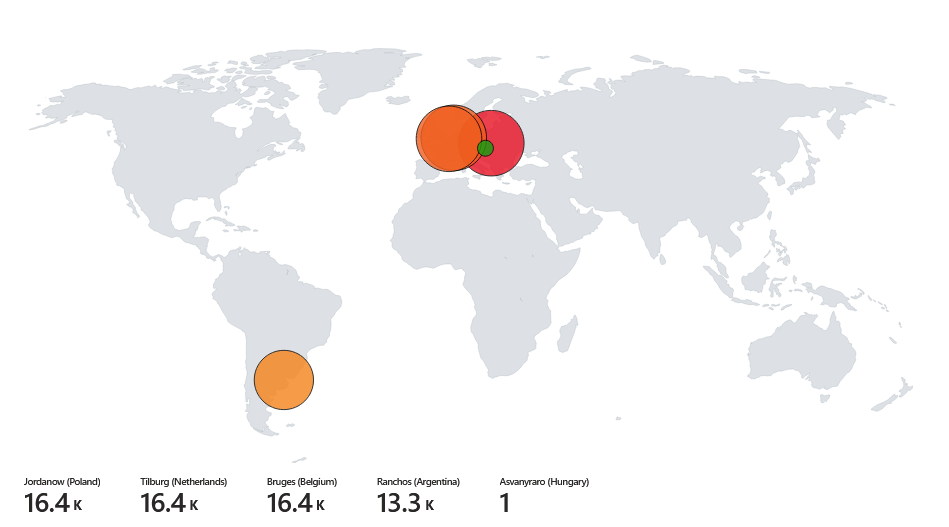
Final Attack Map Results
Here are the results of the brute-force login attempts on my Azure-hosted VM. We can see these are primarily coming from Poland, Netherlands, Belgium, and Argentina.
Key Takeaways
- Learned how to set up and configure a cloud-based SOC using Microsoft Sentinel.
- Gained hands-on experience in log analysis and threat detection.
- Observed real-world attacks on an exposed VM, reinforcing the need for security monitoring.
- Used KQL queries to extract meaningful insights from collected logs.
This project provided valuable exposure to SOC operations, SIEM tools, and cloud-based security monitoring. Thanks for following!